I had fun writing this somewhat tongue-in-cheek dramatization of an actual event. I hope you have as much fun reading it. And yes, it is a blatant ad for our field phone product also.
In the update to my original Defamating post, I pointed out that one of our signs was shot recently, on a trajectory that put one of our buildings and any occupants therein at risk. This happened just as Hurricane Matthew was bearing down on coastal Georgia. While the hurricane itself turned out to be a relative non-event for our area, the power outage was another thing entirely. Our little town was without power for three days, even though very little damage was sustained in this area.
Given this recent violent escalation, we decided to use the hurricane and its aftermath to test some of our equipment and methods. So, we posted a 24-hour watch, including listening posts. These listening posts communicated with the operations center using our field phone sets.
Periodically, I invite various groups to use this facility. Over the years we have hosted amateur radio test sessions, fire department training, and meetings and training for various community defense enthusiasts. As the hurricane was approaching and it seemed as if things might become rough for this area, I notified the local EMA officials, telecom companies and power companies and let them know they could use this facility for personnel, material or as a command center.
For example, the Plant Hatch nuclear power plant is less than 30 miles from the Tattnall EMA command center in Reidsville, and our facility is right on that margin. The wrong puff of wind during an emergency could drive a radioactive plume toward the EMA command center and other backup command posts, but leave our facility untouched (as I wrote this portion, the EMA service sent out a call about a test of the Plant Hatch siren, so the local EMA people take their nuclear preparations seriously).
If the primary and backup EMA command centers were rendered unavailable for any reason, our facility would serve nicely for this, especially since we are located at the connector between the two main east-west corridors through the swamps.
As part of this invitation, I gave the local EMA, telecom and power company supervisors contact protocols to use while entering the facility to make sure that their personnel would not be mistaken for looters. I also extended invitations to regional community defense teams so that if their people, particularly those along the coast, were displaced they would have somewhere to go, since our 7900 square foot brick building has survived almost a century of harsh weather. I gave these teams contact protocols also.
The night after the hurricane grazed the coast, I was manning a listening post. Shortly before midnight, an unmarked and otherwise unremarkable pickup truck rolled through one of our barriers, which had suffered storm damage. Although the driver of this truck executed the first step in the contact protocol, he did not follow-through with the remaining steps. I reported this intrusion to the operations center, where the watchstanders began a discussion of whether to deploy a looter countermeasure known here as The Item. I could hear this discussion over our field phone system.
The Item, being a prototype of a new (presumably) non-lethal concept under development, takes several minutes to deploy, and once deployed, is a wasting asset. It could also only be deployed a limited number of times in the configuration which was available at the time. Since I didn’t think it was a good idea to use this asset for a probing intrusion, which may have also been a lost or confused power company employee, I intended to send the following message to the operations center: DONT WASTE ON PROBING. I began keying the following Morse code message over the field phone’s keyed piezo feature:
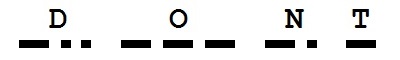
I then was distracted momentarily as the truck began maneuvering around the parking lot, so the remainder of the message was delayed. Without the remainder, what the watchstanders on the other end heard was:
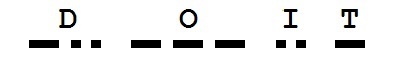
It is unclear whether that was a result of my mis-keying (probably), or their enthusiasm to test The Item in a live contact situation. Regardless, I heard the team begin to move toward preparing to deploy The Item. I then sent the pre-arranged emergency interrupt signal, and corrected my previous with DO NOT WASTE ON PROBING. Preparation of The Item was terminated, and the intruder went on his way, blissfully unaware.
Lessons learned:
– Do coordinate with related parties prior to emergencies, and establish contact protocols. In this case, contact protocols allowed a variety of means, including email, landline, cell phone, amateur radio and visual signals.
– Do establish multiple layers of obstacles to filter out passerby from determined intruders. In this case, our outer barrier was indistinguishable from storm damage, and itself was damaged in ways which we did not sufficiently repair the day prior. Also remember that utility personnel have a legal right, via various easements, to enter property to look for and repair damage to utility infrastructure.
– Do establish escalating alert levels and practice these beforehand. Look for the gaps in these procedures. In this example, an exhausted power company worker, himself under stress and possibly worried about looters as well, might appear at first glance to be a hostile scout. Our response matrix, developed within the context of a relatively constant flow of non-emergency hostile scouting, did not sufficiently anticipate this possibility in an actual emergency.
– Do train or otherwise interact with related parties before an emergency arises. In this case, we had supported training for community defense teams, amateur radio and the fire department ahead of time. Since those groups also include the bulk of the local EMA leadership and that of other community defense teams, most of those people already knew who we are, and that we are reasonably level-headed and rational, cutting back on the possibility of a friendly-fire incident in an actual emergency.
– Do not assume that an approaching party who does not follow the contact protocols is necessarily hostile, but elevate the alert level accordingly in case they are. That is one of the prices that we, as the good guys, pay in an emergency.
– Do not allow the existence of new wunderwaffen (even of the non-lethal variety) to short-circuit the normal command and control procedures established as part of the alert levels.
– Do provide a communication means by which listening posts can remain silent when needed (whispers are easily heard by the bad guys, but easily misunderstood by your own people), yet still remain in the loop for some of the planning and operations. This is an important distinction between neighborhood defense operations versus military operations; in many cases (especially for small teams or early in a crisis before training or experience can catch up) your most experienced people may be standing watches in the field instead of tucked away in a command post. The ability to speak clearly or simply key quietly, depending on the circumstances, is an important advantage.
– Do allow listening posts to finish their transmissions. It is acceptable to begin anticipating the content to help formulate a course of action, but do not let biases (such as the inclination to exploit a technological, personnel or tactical superiority) warp the actual content of the message.
– Do establish an emergency break signal in case information is misunderstood, or circumstances change in the field in such a way that a new, higher priority message can be sent without being blended into the context of the old message.
– Do not use English contractions with unencoded Morse, as nt can easily be mistaken for it, as in do it, can it, would it and so on. We were completely blindsided by this Morse code quirk. Of course, there is an ITU character for apostrophe, but instead of sending that you can just as easily spell it all out. In this case, we were fortunate that the preparation sequence for The Item slowed down the process organically, but this was just blind luck.
Leave a Reply
7 Comments on "Hurricane AAR: Don’t Use Don’t"
[…] Tom explains at his newly-refreshed site. […]
[…] a recent correspondence with Tom Baugh about his AAR following Hurricane Mathew this writer commented that his OPs should have had check points behind them to prevent the […]
[…] a recent correspondence with Tom Baugh about his AAR following Hurricane Matthew this writer commented that his OPs should have had check points behind them to prevent the […]
[…] a recent correspondence with Tom Baugh about his AAR following Hurricane Matthew this writer commented that his OPs should have had check points behind them to prevent the […]
[…] with different off-grid solar power configurations for a while. As I have mentioned in a previous article, power went out for three days in the aftermath of Hurricane Matthew. This gave us an excellent […]
[…] ten, including an awesome guest post by SFC Barry with an important and informative critique of our Hurricane Matthew AAR. We’re looking forward to more guest articles, including some I’ve been sitting on by […]
[…] and counter-revolutionary.IntroductionDuring a recent correspondence with Tom Baugh about his AAR following Hurricane Matthew this writer commented that his OPs should have had check points behind them to prevent the […]